The latest scam alerts from Which?

Find out about the latest scams trending this month. Come across a scam? Let us know by using our scam sharer tool.
Join over half a million Scam Alert subscribers and get free weekly updates on the scams you need to be aware of. In just five years, Which? Scam Alerts has helped subscribers to avoid almost £5.5m in scam losses.
13 May
Barclays scam text
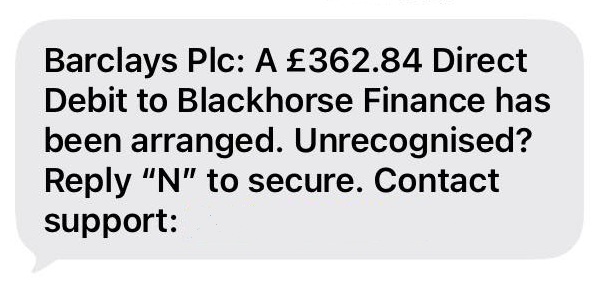
A scam text impersonating Barclays from a spoofed mobile number tells you that a direct debit has been arranged.
It goes on to provide a number to call, which will most likely put you through to a scammer who'll try to get you to reveal your personal and financial information.
Scam texts like this can be reported by forwarding them to 7726.
11 May
Scam FCA text
Text messages claiming to be from the Financial Conduct Authority (FCA) claim that your details were identified in a Report Fraud report and your personal data is at risk due to a data breach.
It gives you a number to call and reports suggest that if you call the number and you will be asked for your first and last name, who you bank with and your current balance.
One report also said they were given a 5 digit reference code to quote when called by a 'manager' to verify fraudulent activity.
Scams like these typically encourage you to give personal and financial information.
Scam texts can be reported by forwarding them to 7726.
5 May
Dodgy car finance text
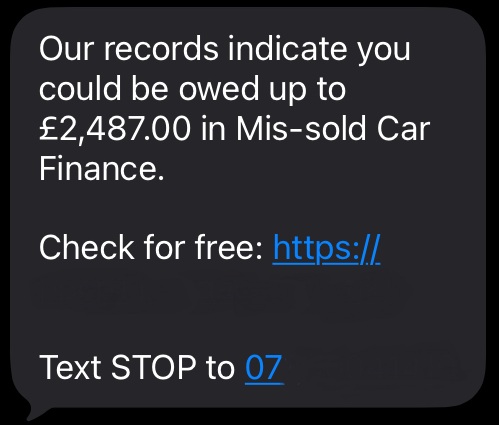
A scam text sent from a claims management firm tells you that you could be owed up to £2,487 in mis-sold car finance and provides a link to see how much you're owed.
It also includes a number to text to stop receiving messages. On Who Called Me, reports of this number claim receiving the text despite not being owed any money.
Drivers who were mis-sold car finance are now due compensation and rogue claims firms are cropping up.
You can search the Financial Conduct Authority's (FCA) register to see if a company can legally provide financial services in the UK.
Scam and spam texts can be reported by forwarding them to 7726.
27 April
TV Licence scam email
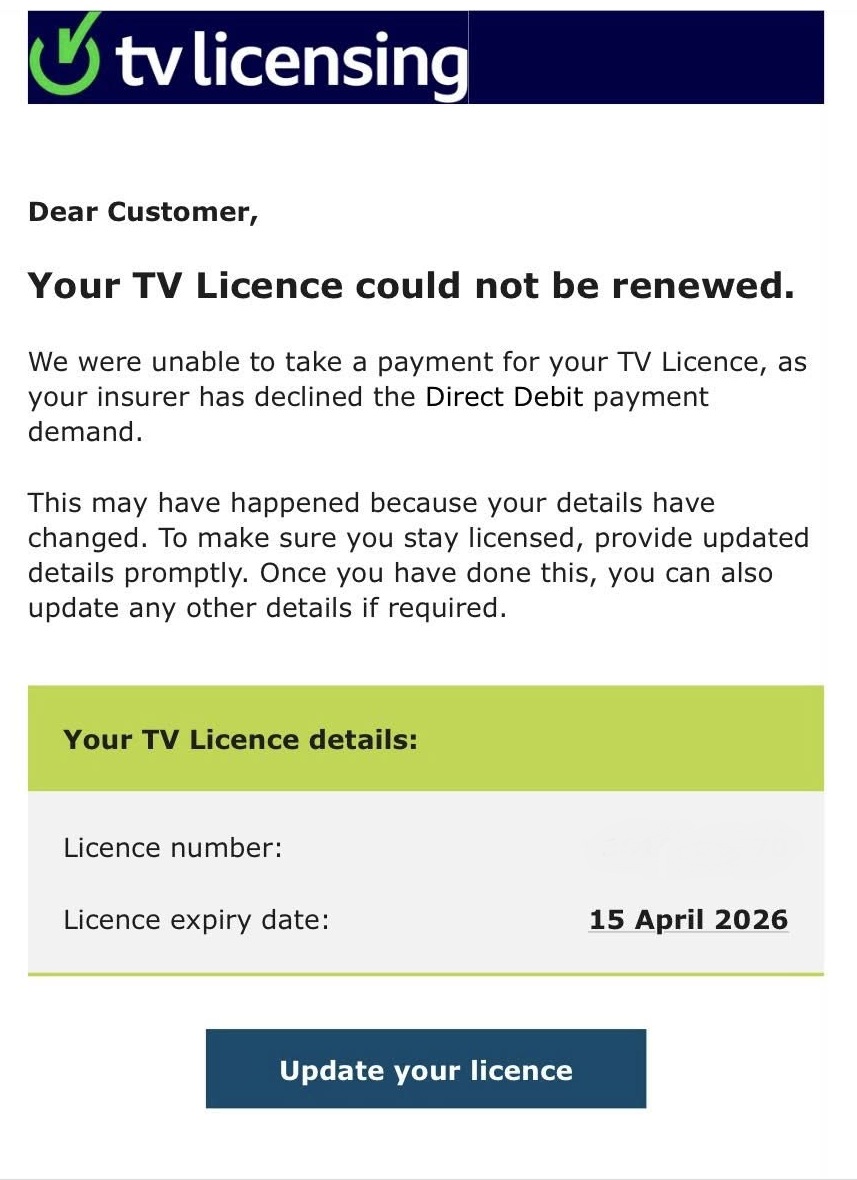
A scam email impersonating TV Licensing tells you that your TV Licence could not be renewed and provides a link to start the renewal process.
The email also says that your direct debit payment has been declined and is sent from a '.jp' domain, which is a Japanese-registered email address.
The link included in it will lead to a phishing website intent on stealing your personal and payment information.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
Phishing websites can be reported to the National Cyber Security Centre.
21 April
Apple scam text
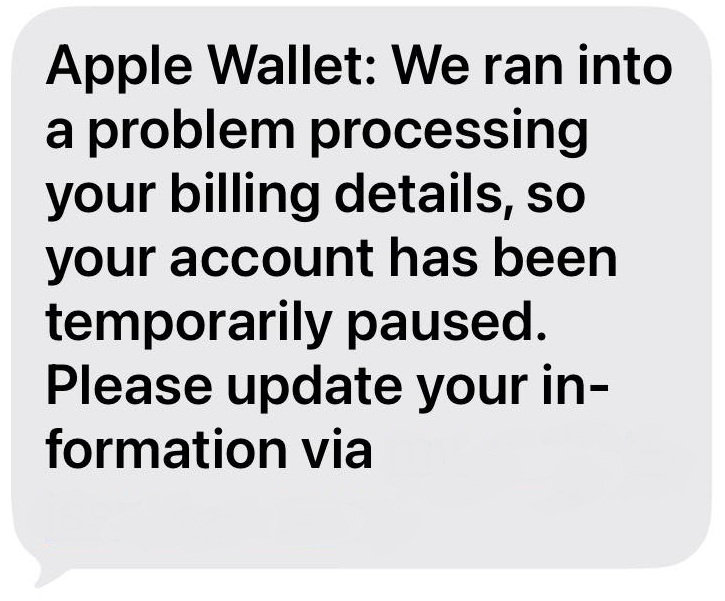
A text which claims to be from Apple tells you that there was a 'problem processing your billing details.'
It also says that your account is temporarily paused and provides a phishing link to rectify this.
This will lead to a website which will steal your personal and financial information after you enter it in.
Scam texts can be reported by forwarding them to 7726 and scam websites can be reported to the National Cyber Security Centre.
13 April
National Rail impersonation email
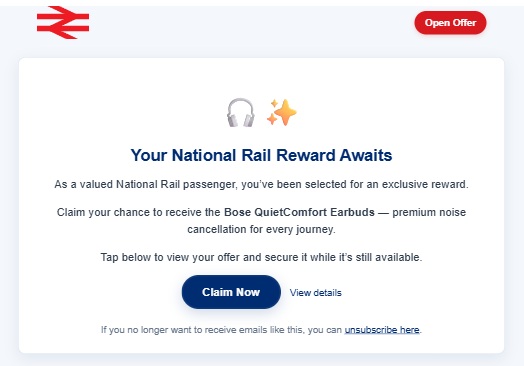
An email impersonating National Rail tells you that you're in with a chance of getting a pair of earbuds for being a 'valued National Rail passenger.'
It provides a link to 'claim' these which will probably lead to a dodgy website, set up to gather your personal details.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
Phishing websites can be reported to the National Cyber Security Centre.
Fortnum & Mason scam email
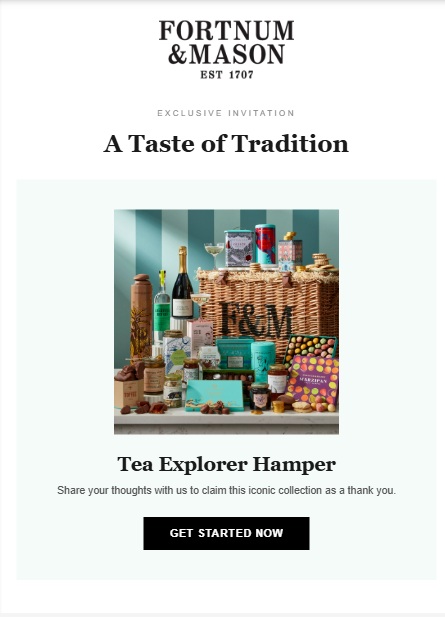
A dodgy email claiming to be from Fortnum & Mason tells you that you're eligible for a 'Tea Explorer Hamper' by following a suspicious link.
This will most likely lead to a phishing website created to steal your personal and payment details when you enter it in.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
Phishing websites can be reported to the National Cyber Security Centre.
31 March
Car finance claims scams
Watch out for scammers taking advantage of the Financial Conduct Authority's car finance compensation scheme.
Which? is aware of dodgy texts, emails and websites claiming that you're owed compensation for mis-sold car finance.
The aim of this scam is to trick you into sharing your personal and sensitive information.
Scam texts can be reported by forwarding them to 7726, scam emails can be forwarded to report@phishing.gov.uk and scam websites can be reported to the National Cyber Security Centre.
30 March
DPD delivery scam
Which? is aware of a DPD delivery text scam circulating.
Versions of this message are likely to warn that there has been a missed delivery that you need to rearrange or an unpaid fee.
The message will instruct you to reply to the text, or follow a link to give further information or card details. Some will use very convicing copycat websites, such as in this version of a DPD scam that we warned about in August 2021.
Do not reply to the message or follow any link. Report the message to 7726, a free reporting service run by phone operators.
If you are concerned it could be genuine, visit the DPD website directly and use verified contact details or tracking information from its website.
25 March
Garden waste subscription scam
Bassetlaw District Council, a council in Nottinghamshire, has warned residents of fake garden waste subscription leaflets being posted.
The leaflets feature QR codes to scan, which could lead to phishing websites or malware being downloaded to your device.
Phishing websites can be reported to the National Cyber Security Centre.
23 March
Evri copycat site
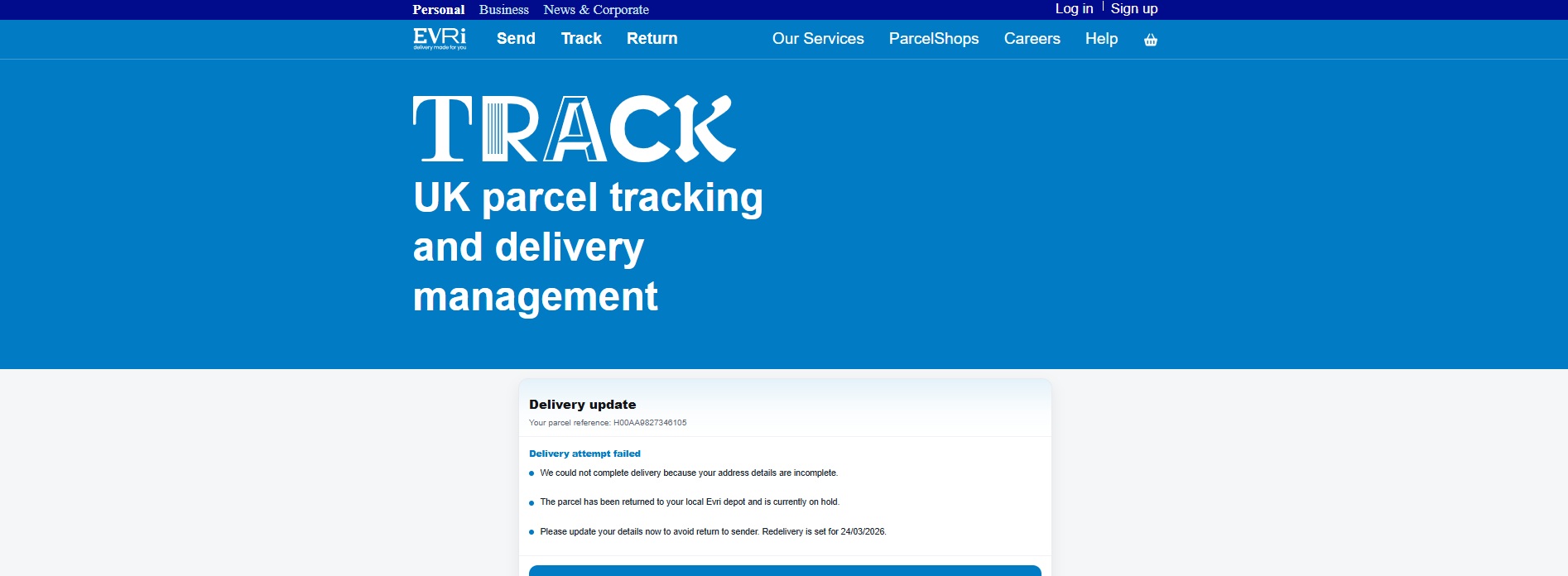
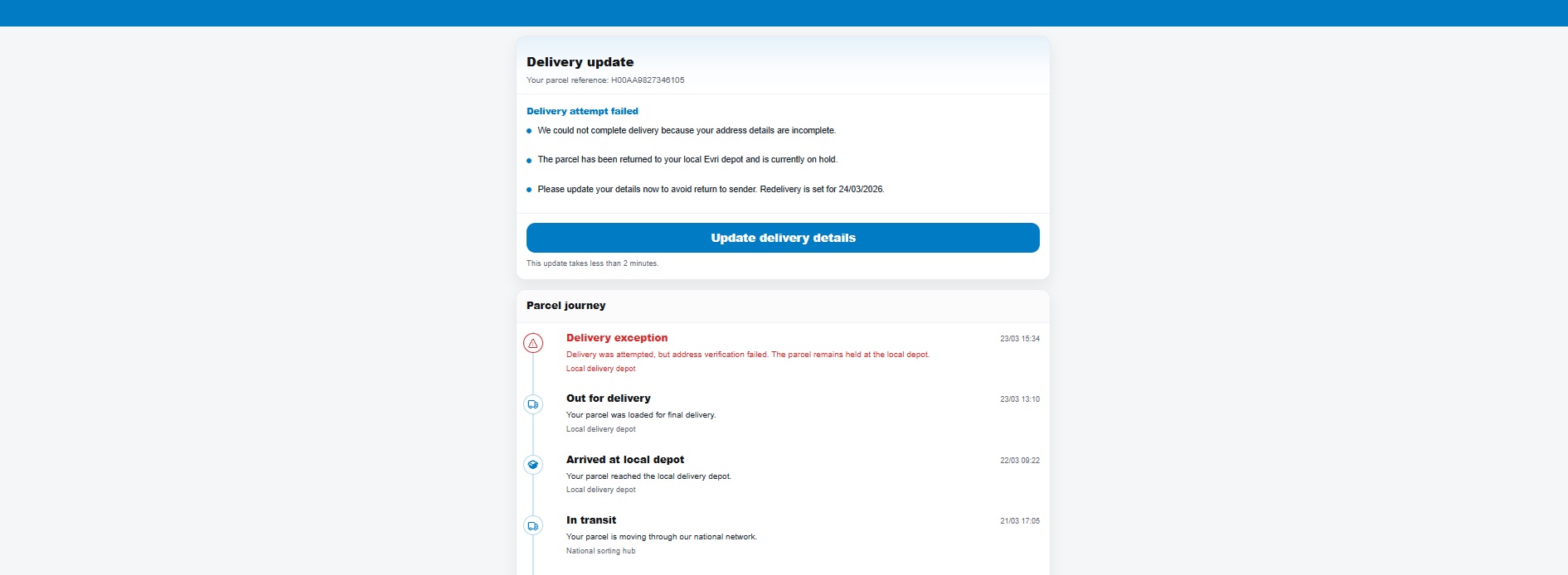
A scam text which says that your delivery failed due to a signature being required provides a link to reschedule the delivery.
This link leads to a convincing Evri copycat site complete with up to date logos and branding.
Entering your personal information into sites like these leaves you vulnerable to being scammed in the future, as fraudsters can use these details to make their scams more convincing.
Scam texts can be reported by forwarding them to 7726 and scam websites can be reported to the National Cyber Security Centre.
Account closure scam
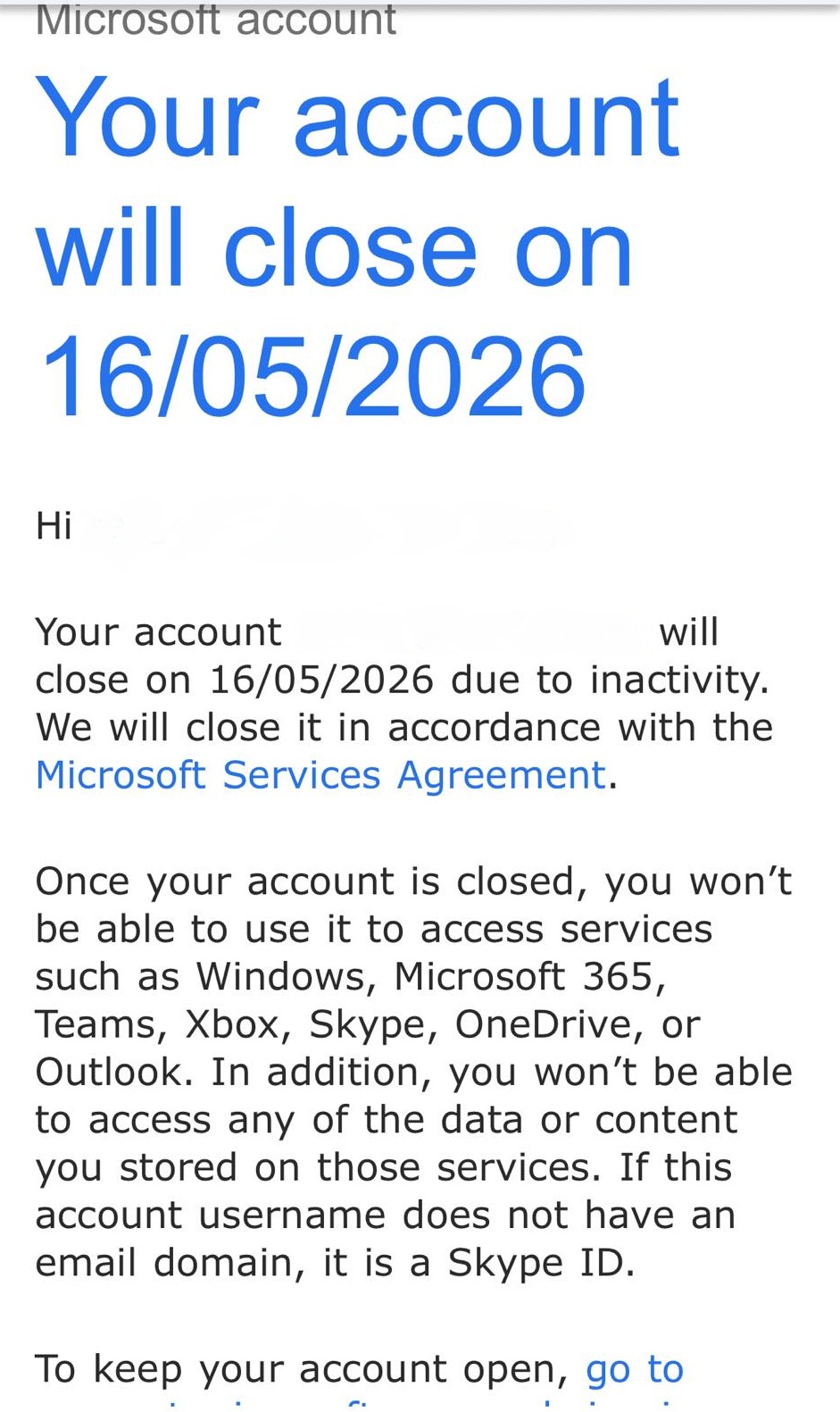
A scam email impersonating Microsoft tells you that your account will close due to 'inactivity.'
It goes on to say that you won't be able to access any Microsoft services including Windows and Outlook, or access any of your data stored on these services.
The email also includes a link to 'keep your account open' which will most likely lead a phishing site intent on stealing your personal details.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
Scam websites can be reported to the National Cyber Security Centre.
16 March
Marriott Hotel impersonation email
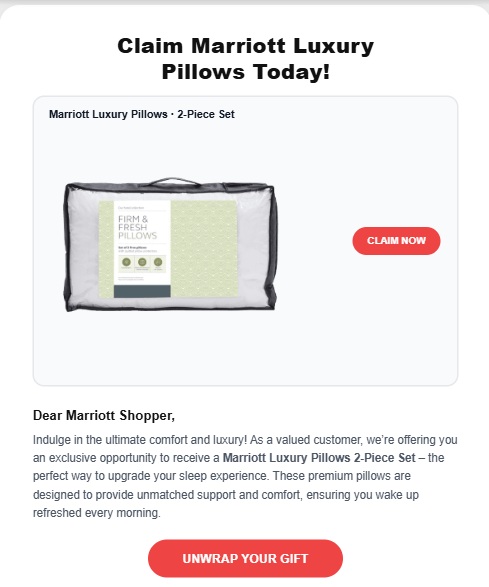
A scam email claiming to offer 'Marriott luxury pillows' includes a dodgy phishing link.
Following this link will lead to site that will steal your personal and financial information after you enter it in.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
Scam websites can be reported to the National Cyber Security Centre.
11 March
Cloud Storage scam
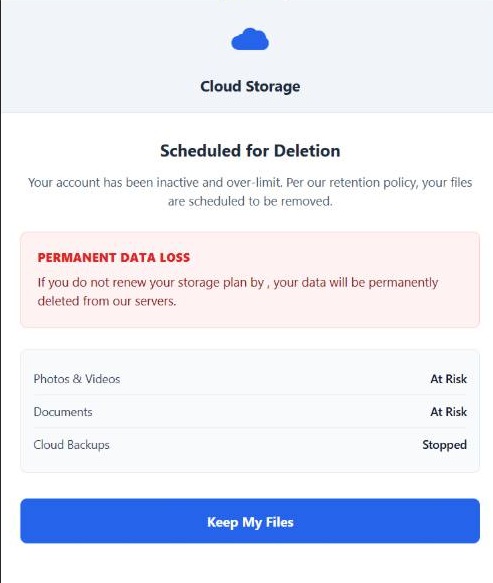
A scam email tells you that your account is scheduled for deletion and that you face 'permanent data loss' of your files.
This is a fake email attempting to worry you into following a dodgy link.
The link will lead to a website that will steal you personal data or download malware to your device.
Scam emails like this can be reported by forwarding them to report@phishing.gov.uk
3 March
Scammers impersonate Wiltshire Police
Fraudsters are claiming to be from Wiltshire Police and calling residents to tell them a package is being held as part of an investigation.
In this scam, the fraudsters will give you a made up crime reference number and told you'll be called by your bank.
Then you'll be called by the same scammers, but this time, they'll be impersonating your bank and will go on to request access to your account.
You should never disclose financial details to callers over the phone.
On an iPhone, you can report scam calls to your provider by texting the word ‘call’ followed by the phone number to 7726.
If you have an Android phone, text the word ‘call’ to 7726. You’ll then receive a message asking you for the scam number.
23 February
Norton scam email
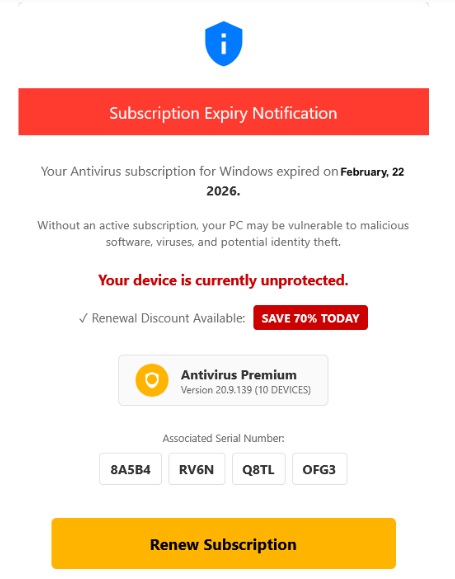
A malicious email claiming to be from cybersecurity company Norton tells you that your subscription to the software has expired and therefore, your device is vulnerable to 'malicious software,' 'viruses' and 'identity theft.'
It goes on to promote a 70% discount on the subscription service and gives you a link to 'renew' it.
This link will lead to a dodgy website which will either steal your personal details or download malware to your device.
You can report scam emails like this by forwarding them to report@phishing.gov.uk and suspicious websites to the National Cyber Security Centre.
16 February
Scam 'Hi mum' text
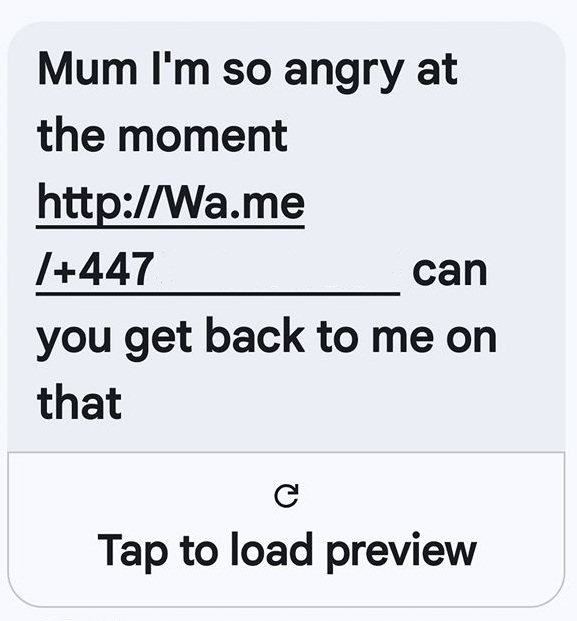
The 'Hi mum' text is a scam message that continually does the rounds and sees scammers posing as adult children.
In a new version of the scam, the text addresses the recipient as mum and attempts to continue the conversation on WhatsApp.
Here, the scammer will make up an emergency scenario in an attempt to get you to transfer them money.
You can report scam texts by forwarding them to 7726.
11 February
Mail Online impersonation scam

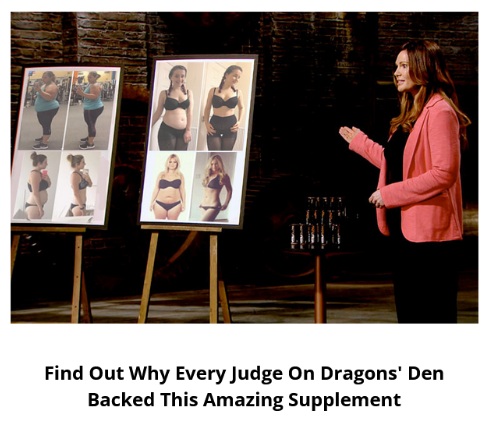
A dodgy email impersonating the Daily Mail website and Dragons' Den claims to offer an 'amazing weight loss supplement.'
The email goes on to include a link to buy the product, which will lead to a malicious website designed to steal your personal and financial information.
You can report scam emails like this by forwarding them to report@phishing.gov.uk and suspicious websites to the National Cyber Security Centre.
9 February
Which? scam accounts on X

On X, formerly known as Twitter, fraudsters were impersonating Which? through the account handles @whichukrep and @WhichukAsk.
Accounts like these will try and get you to reveal personal and financial information.
Which? reported these accounts and they have now been suspended. You can report accounts on X by selecting the three dots on the account page and pressing report.
Which?'s official X account is @WhichUK.
Apple scam email

A dodgy email impersonating Apple tries to get you to act quickly by telling you that 'your system is heavily damaged by viruses.'
It goes on to provide a link to 'remove viruses' which could lead a phishing website or malware being downloaded to your device.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
2 February
Cleaning Superstore WhatsApp scam
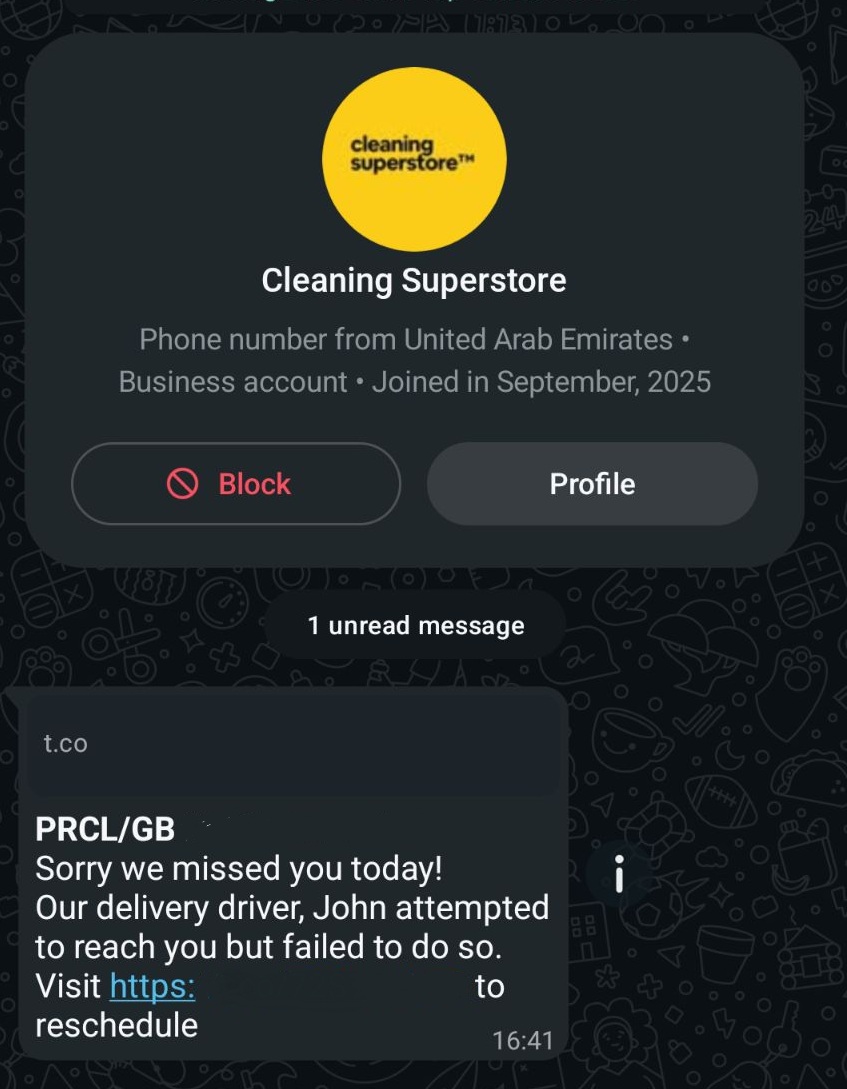
A scam circulating WhatsApp appears to have hijacked a legitimate WhatsApp business account to spread a delivery scam.
Which? has previously reported on this type of scam which saw another compromised business account be used by fraudsters to send out 'missed delivery' scam messages.
WhatsApp messages sent from Cleaning Superstore, a genuine business located in the UAE, tell you that you've missed a delivery and provide a dodgy link to reschedule.
This link will lead to a malicious site set up to steal your personal and financial information after you enter it in.
To report a WhatsApp user, open up the chat, tap on the sender's contact details and select 'block and report'.
28 January
New card scam text
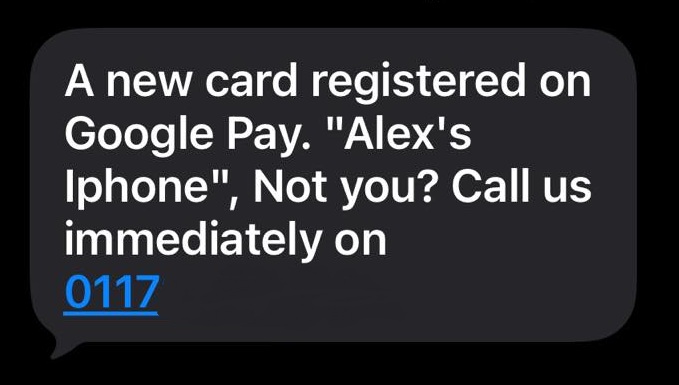
A text from a random mobile number tells you that someone else's card has been registered on your Google Play account.
It then gives you a number to call if you didn't do this. Calling this number will lead to a scammer asking you questions to try and gather personal and financial information.
Recipients of this scam text have also reported the text saying that a new card had been added to their Apple Pay account or Apple Wallet.
Scam texts can be reported by forwarding them to 7726.
27 January
Microsoft 'Power Bi' scam
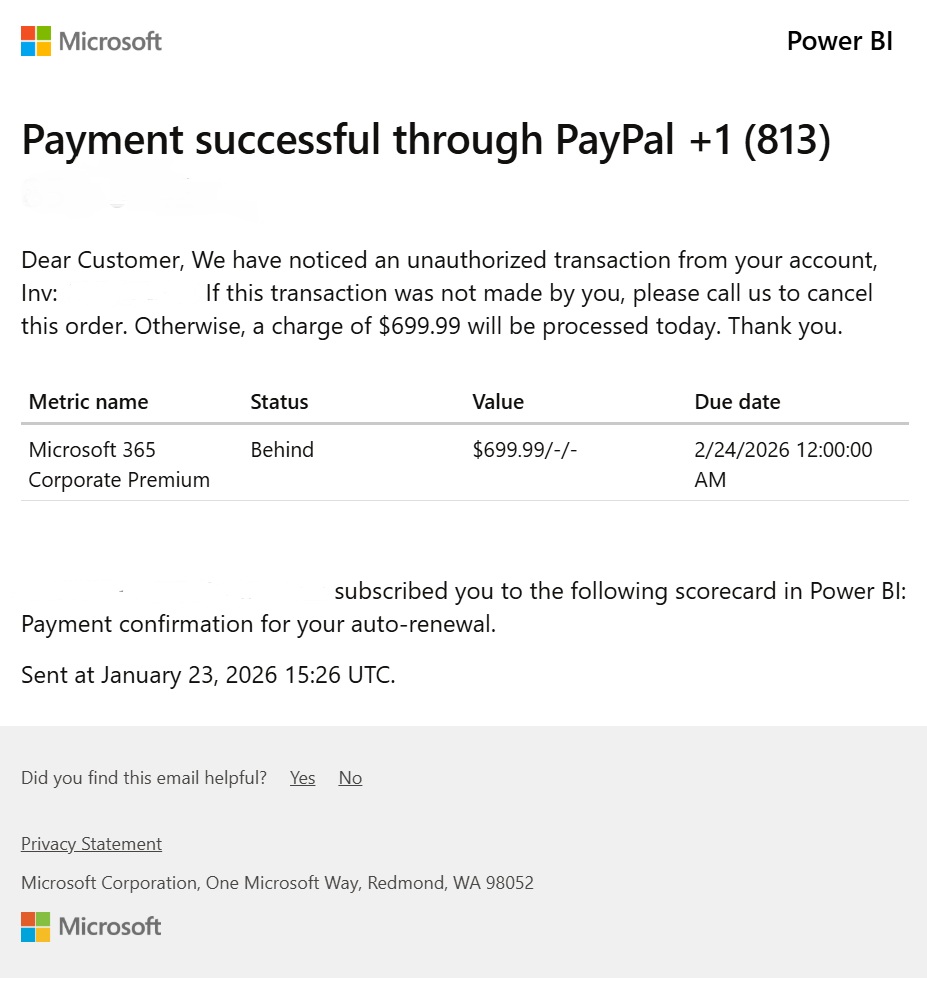
A scam email impersonating Microsoft sent from 'no-reply-powerbi@microsoft.com,' tells you that an authorised transaction has been made on your account.
It gives you an international number to call if you didn't make this.
Calling this number will put you through a fraudster who will ask you questions in an attempt to elicit your personal and financial details.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
21 January
British Gas scam email
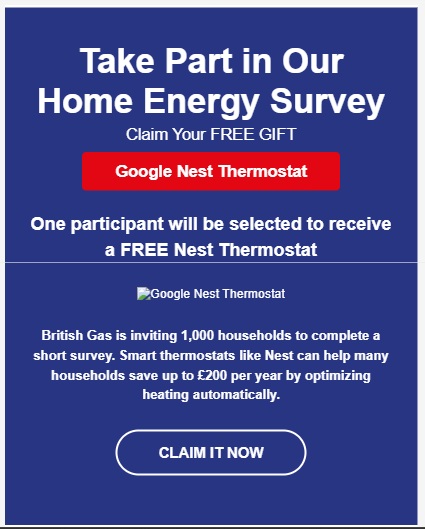
An email which claims to be from British Gas tells you that you have the opportunity to receive a Google Nest thermostat.
It goes on to say that in order to receive the thermostat, you need to follow a link to complete a short survey.
This link will lead to a dodgy site which will steal your personal data as you enter it in and use this to scam you now or in the future.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
Dodgy websites can be reported to the National Cyber Security Centre.
19 January
Royal Mail impersonation scam
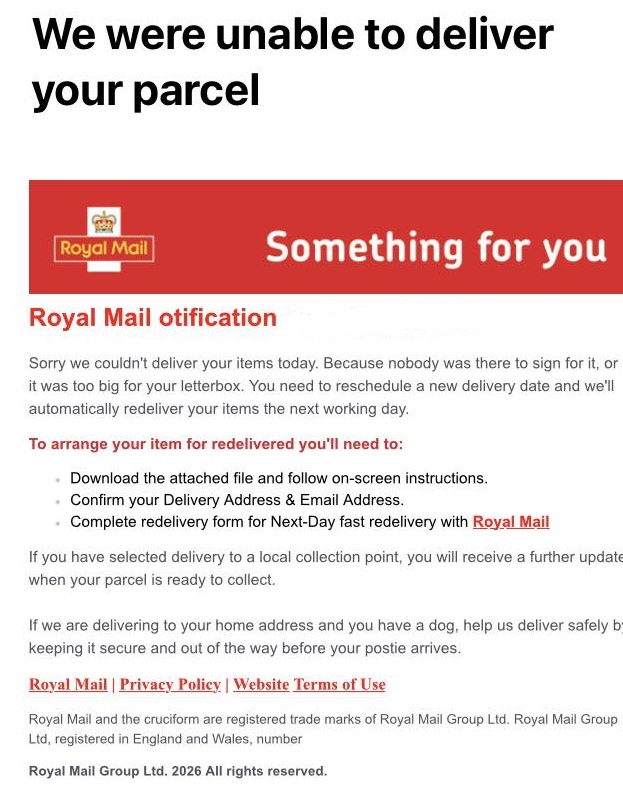
A dodgy email claiming to be from Royal Mail tells you that you've missed a delivery.
It goes on to say that you need to reschedule the delivery by downloading an attachment on the email and 'following on-screen instructions.'
This could lead to malware being downloaded to your device, which can steal your personal information. It could also phish for your personal and financial info by asking you to fill in personal details to reschedule the delivery before stealing them.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
14 January
Royal Bank of Scotland scam email

A dodgy email claiming to be from the Royal Bank of Scotland tells you that a new direct debit has been set up on your account.
It goes on to detail where this direct debit will be sent to and how much it is.
The email also gives you a number to call if you didn't authorise this payment, which will put you straight through to a scammer who will try to get you to reveal personal information.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
12 January
EE points scam

A scam text claiming to be from mobile operator EE tells you that you have thousands of 'EE Points' which, once redeemed, offer 'exciting rewards.'
The message includes a link to redeem these points, which leads to a copycat EE website waiting to grab your personal data. The message also says that the points are about to expire in an attempt to get you to act quickly.
Which? has previously warned of these text messages, which EE confirmed were fraudulent.
Scam texts can be reported by forwarding them to 7726.
Dodgy websites can be reported to the National Cyber Security Centre.
5 January
NatWest scam email
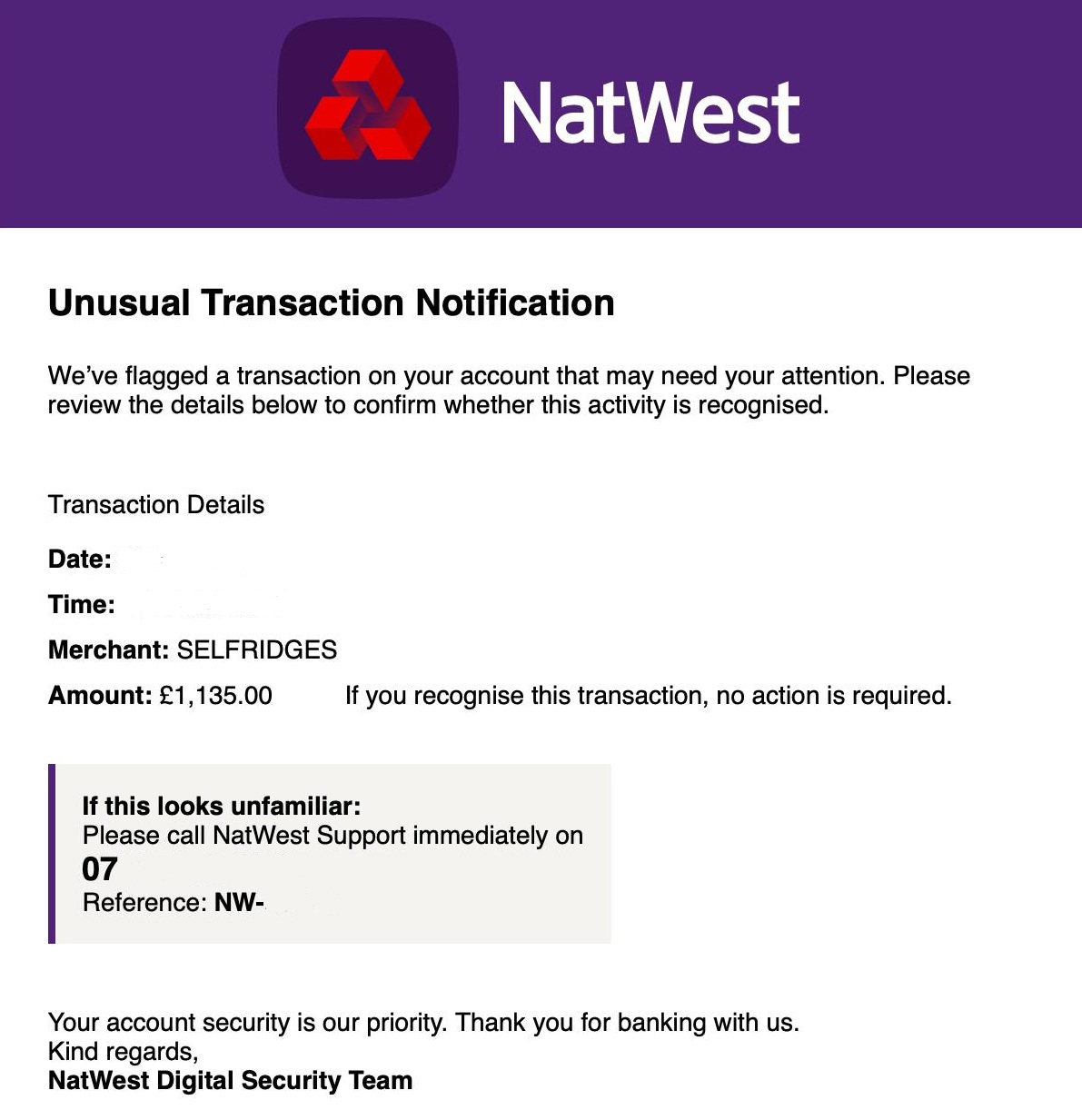
A scam email which claims to be from NatWest tells you that there's been an 'unusual transaction' on your account.
The email goes on to list the amount spent and where it was spent in order to get you to panic and act quickly.
It also provides a mobile number for you to call if the transaction is unfamiliar, which is not linked to NatWest. Calling this number will likely connect you with a scammer intent on manipulating you into revealing your personal and financial information.
You can see your recent bank transactions by logging into online banking. If there is anything you're unsure about, call your bank using the number on the back of your bank card.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
29 December
Wise impersonation email

Scam emails pretending to be from online bank Wise tell you that some features on your Wise account have been restricted and use accurate branding to appear legitimate.
The emails include a link to 'complete your account review,' claiming that you need to do this to be able to send and receive money using your Wise account.
One of the giveaways that this is a scam email is that it is sent from a random email address, containing random numbers and letters. Hovering over the links also reveals that they don't lead to the official Wise website.
If you are a Wise customer and receive this email, log in to your account by independently visiting the official Wise web address and verifying the information that way.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
Dodgy websites can be reported to the National Cyber Security Centre.
22 December
Most reported purchase scams
Purchase scams are when you buy a product online and receive nothing in return or something that isn't as described.
Lloyds Bank has revealed the top five most reported purchase scams in 2025, according to its customer data as:
- Vehicle and vehicle accessories
- Ticket scams
- Clothes and accessories
- Personal items (e.g. perfume, hair extensions)
- Driving lessons and tests
The bank also predicts that ticket scams will be big in 2026 and found that more than 70% of purchase scams happen on Meta-owned platforms.
To report scam ads or posts on Facebook or Instagram, select the three dots in the top right corner and press report.
17 December
NatWest scam email
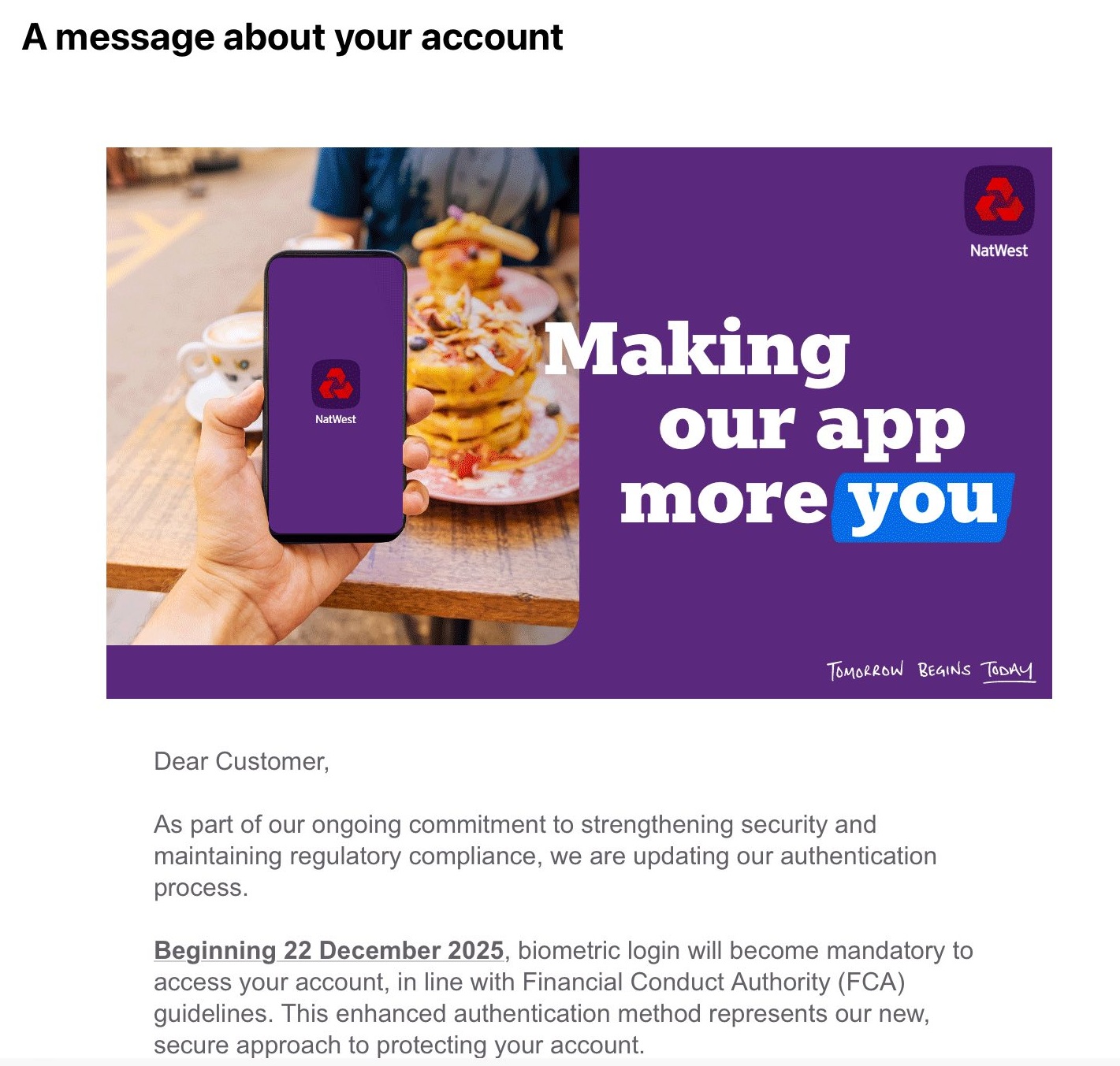
A scam email which claims to be from NatWest tells you that the Financial Conduct Authority (FCA) will be making biometric login, using a biological trait like your fingerprint, mandatory.
This isn't true. The FCA does require banks to implement Strong Customer Authentication (SCA), such as getting you to enter in a one-time passcode sent to your phone before logging into online banking on a computer, but biometric checks aren't mandatory.
Scammers have used this lie to coax you into clicking on a malicious link and parting with your personal and financial data.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
Dodgy websites can be reported to the National Cyber Security Centre.
9 December
Costa Coffee scam
Trading Standards services across the country are warning of a scam email impersonating Costa Coffee.
The email claims that you're in with the chance of winning a Yeti Rambler Tumbler, complete with a link leading to a phishing website that will steal your personal and financial information.
You can report scam emails like this by forwarding them to report@phishing.gov.uk.
Dodgy websites can be reported to the National Cyber Security Centre.
3 December
Arthritis UK scam calls
Arthritis charity Arthritis UK has warned of a wave of scam calls claiming to be from the organisation.
The calls tell you that you're eligible for help with the completion of benefits forms in return for a fee, but this isn't the case, and you never should pay to fill out benefit forms for support you're eligible for.
You can report phone scams on your mobile by forwarding the number to 7726.
On WhatsApp, find the number on your call log, select the 'i' and then 'report.'
1 December
Postcode Lottery scam email
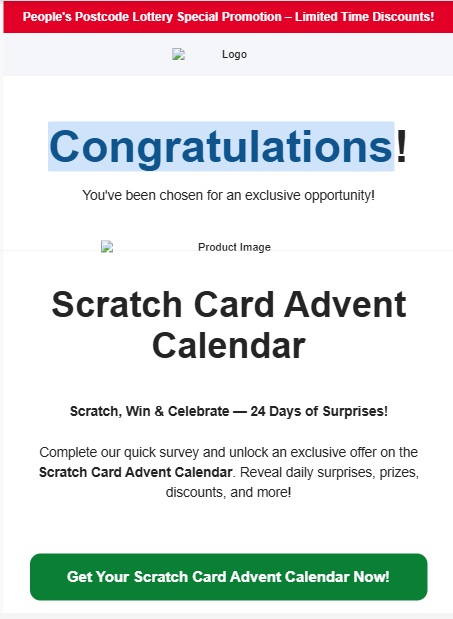
A dodgy email impersonating the People's Postcode Lottery telling you you've won a 'scratch card advent calendar' with daily 'surprises, prizes and discounts' is circulating.
You're encouraged to follow a link to complete a survey to receive the advent calendar, which will lead to a malicious website designed to grab your personal and financial details.
The People's Postcode Lottery has also warned of this scam, stating that this email isn't from them and they would never ask you for any form of payment before claiming a prize.
Scam emails can be reported by forwarding them to report@phishing.gov.uk.
Dodgy websites can be reported to the National Cyber Security Centre.
24 November
Amazon scam text
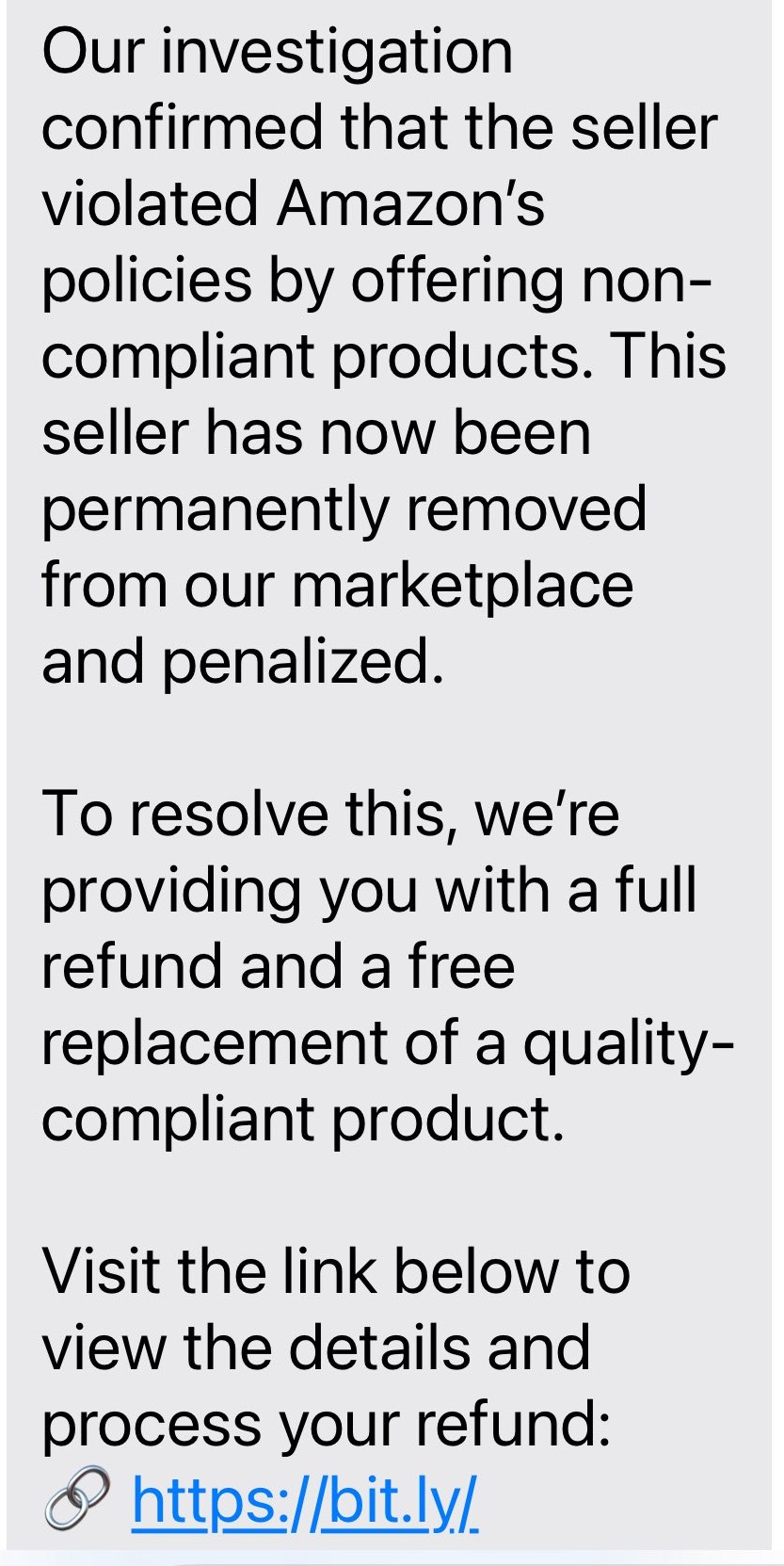
A scam text claiming to be from Amazon tells you that you've been given a full refund following an 'investigation into a seller violating Amazon's policies.'
The text is sent from a random, likely spoofed, mobile number and includes a link to a convincing copycat Amazon page which was created in March this year.
This page asks for your Amazon login information, which will hand them over to a fraudster.
Scam texts can be reported by forwarding them to 7726.
Dodgy websites can be reported to the National Cyber Security Centre.
17 November
Morrisons scam ad
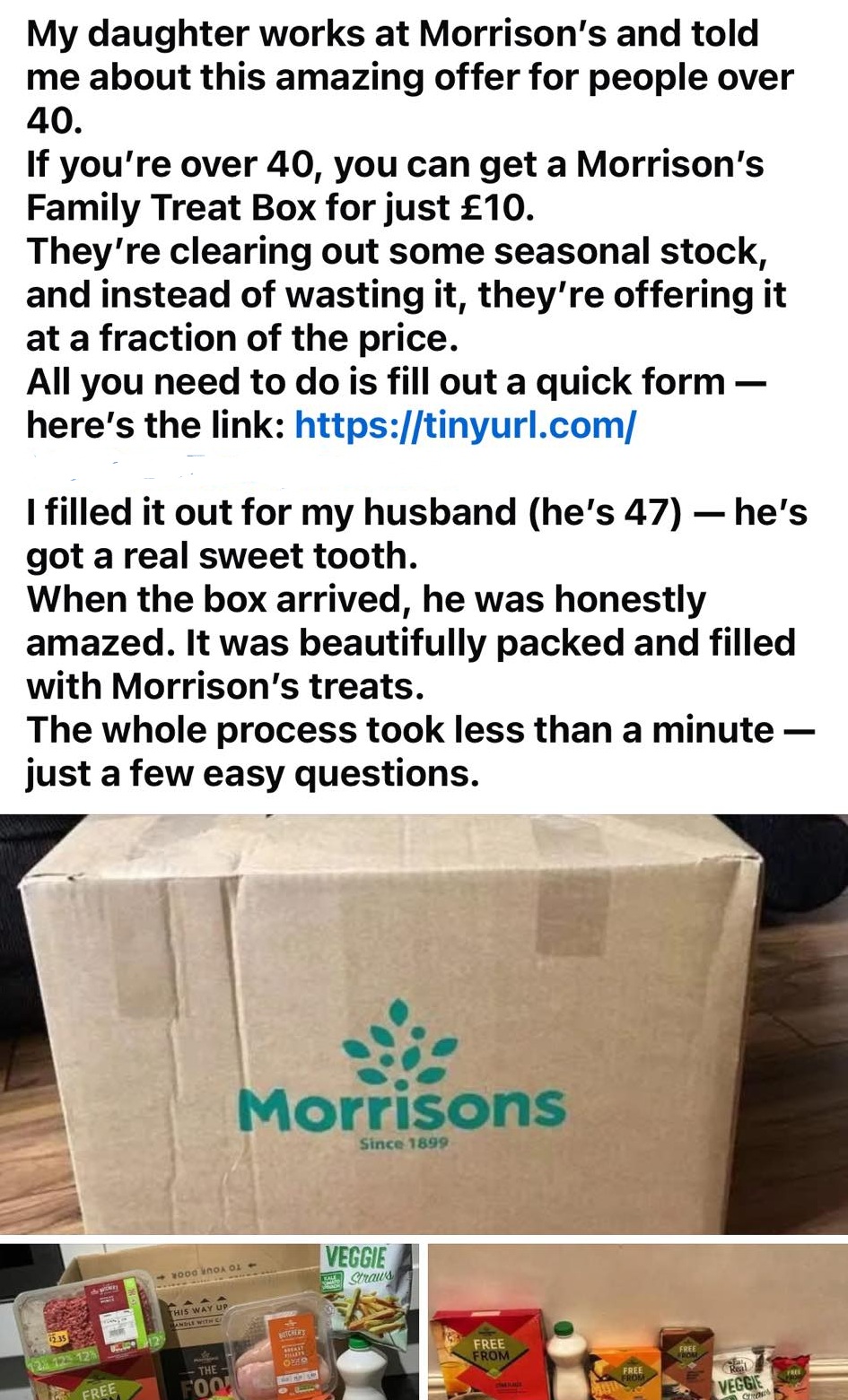
An advert on Facebook, claiming to be posted by a person whose daughter works at Morrisons, offers a 'family treat box' for just £10 for people over 40.
It goes on to give you a link to fill out a form in order to receive the treat box.
This will lead to a website designed to steal your personal details.
You can report scam ads on Facebook by selecting the three dots in the top right corner and pressing report.
Phishing websites can be reported to the National Cyber Security Centre.
10 November
Loft insulation scams
Dodgy unsolicited calls about loft insulation are circulating.
Recipients of such calls have claimed of being asked if they have white fluffy stuff in their loft, told that their property has been identified as having loft insulation that would cause condensation and damp and being offered free loft insulation services.
Which? has previously reported on fraudsters targeting people in spray foam loft insulation scams.
You can report phone scams on a mobile by forwarding the number to 7726.
On WhatsApp, select the 'i' next to the number, scroll down and press report.
4 November
'Goat Agency' scam text

A dodgy text message falsely claims to be from marketing company The Goat Agency and offers a 'flexible remote job providing product reviews.'
These scam texts impersonate legitimate companies to appear genuine and always offer easy task-based work with high salaries.
At first you'll see earnings for your work, before being asked to invest in more money to complete tasks where the earning potential is higher.
You'll never get any money you put into the job back and you'll never be able to retrieve your earnings.
Report scam texts like this to your mobile provider by forwarding them to 7726.
30 October
Fake Sports Direct website

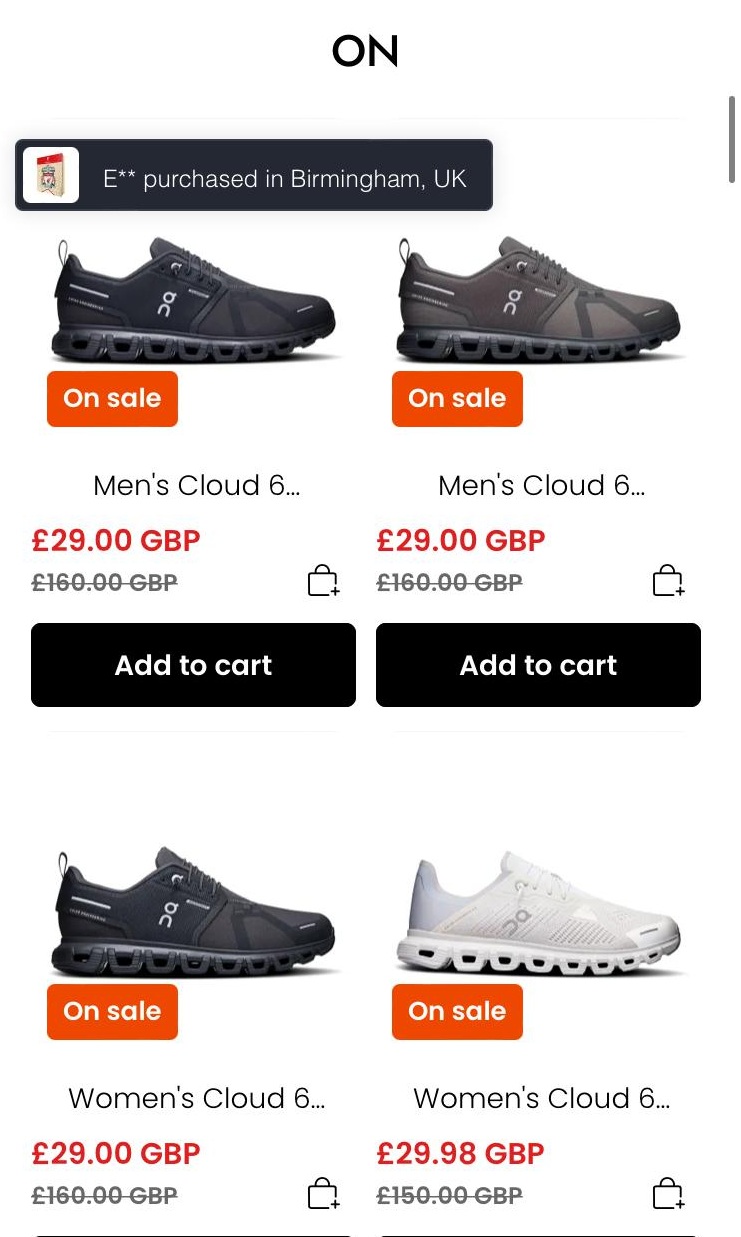
A copycat website impersonating Sports Direct lists heavily discounted items to look genuine and asks for your personal and payment information to purchase products.
It uses the retailer's branding to appear legitimate. Which? also found the website was only created earlier this year.
If you enter this information you'll be handing it straight to the scammer.
If you spot a site like this, report it to the National Cyber Security Centre and contact your card provider if you've already entered payment details.
29 October
Disney scam email
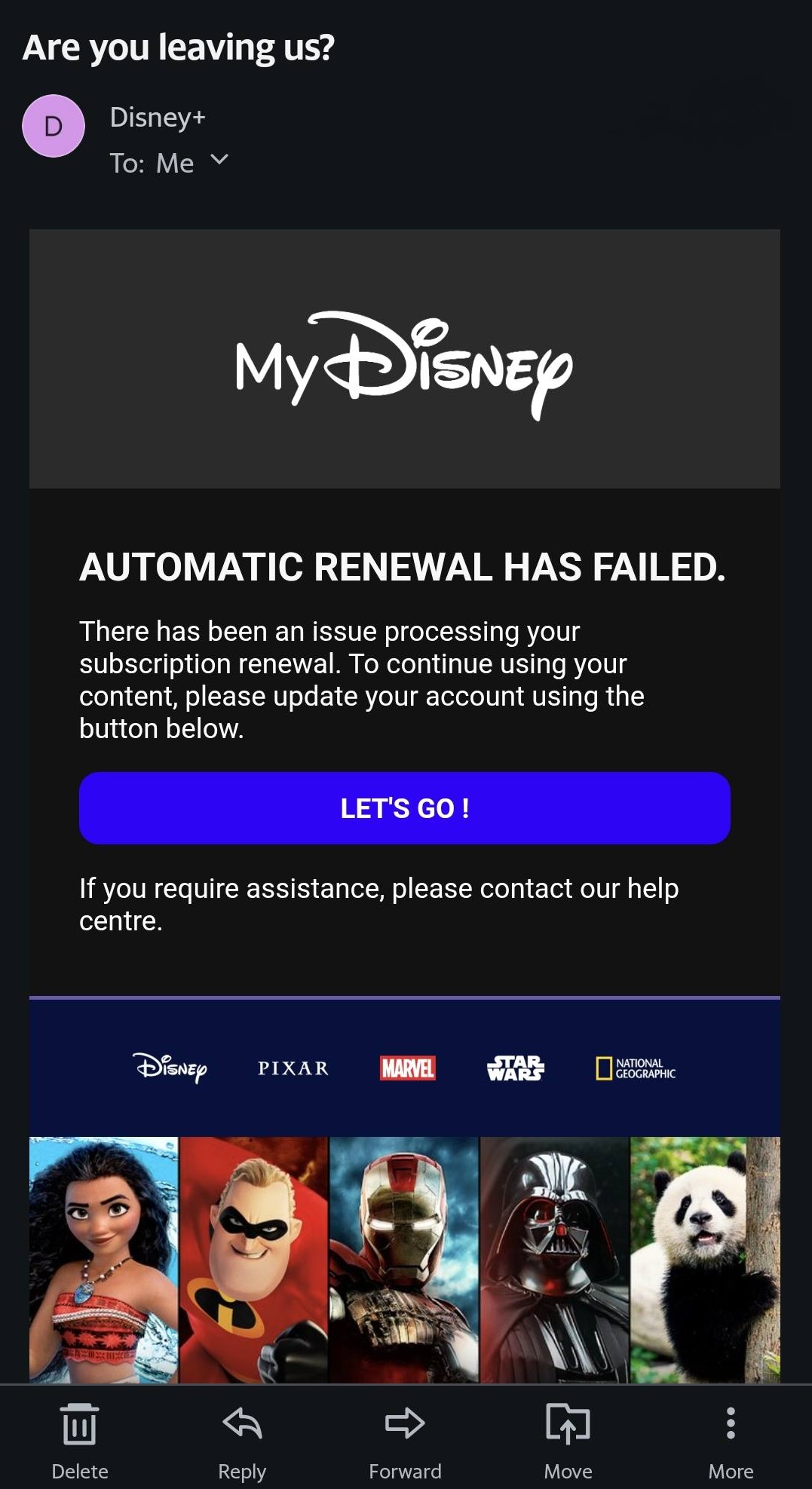
A suspicious email that claims to be from Disney tells you that there's been an issue renewing your subscription to the streaming service and to follow a link to rectify this.
This link will lead to a malicious website designed to steal your personal and financial information.
Dodgy emails can be reported by forwarding them to report@phishing.gov.uk.
Phishing websites can be reported to the National Cyber Security Centre.
28 October
McAfee impersonation email
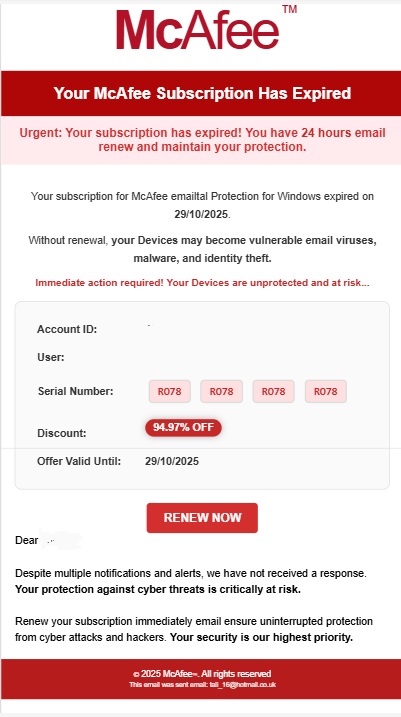
Scammers are continuing to impersonate security brands in phishing emails.
One of the latest versions claims to be from McAfee and tells you that your subscription has expired and you have '24 hours to maintain your protection.'
It also includes a link to 'renew now' which will lead to a dodgy site designed to get you to enter in your personal and payment information.
Scam emails can be reported by forwarding them to report@phishing.gov.uk.
Phishing websites can be reported to the National Cyber Security Centre.
21 October
Netflix scam email
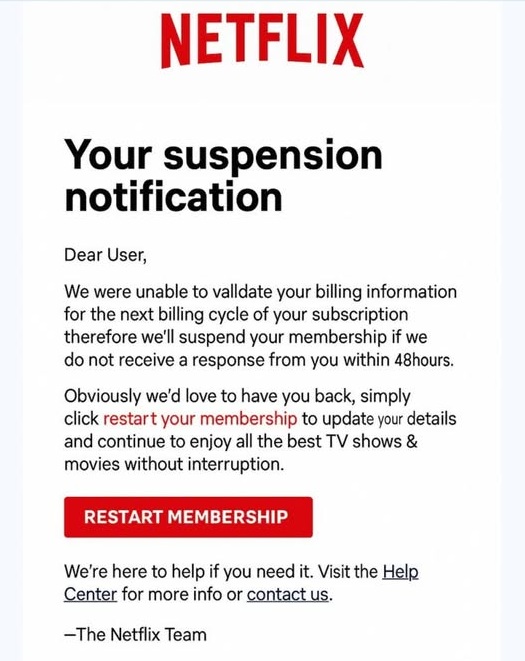
A dodgy email impersonating Netflix titled 'suspension notification' warns you that you need to update your details in order to keep using the service.
It claims that your billing infomation couldn't be 'validated' and encourages you to follow a link to do this within '48 hours'.
This link will lead to a malicious site that will steal your personal information after entering it in.
Scam emails can be reported by forwarding them to report@phishing.gov.uk.
Phishing websites can be reported to the National Cyber Security Centre.
20 October
Royal Mail scam text

Scam texts impersonating Royal Mail tell you: 'Your parcel has been temporarily held due to an unclear or invalid delivery address'.
It includes a malicious link to follow to 'verify your address.' The link will lead to a site posing as Royal Mail in order to grab your personal information after you enter it in.
Scam texts can be reported by forwarding them to 7726.
15 October
DVLA text scam
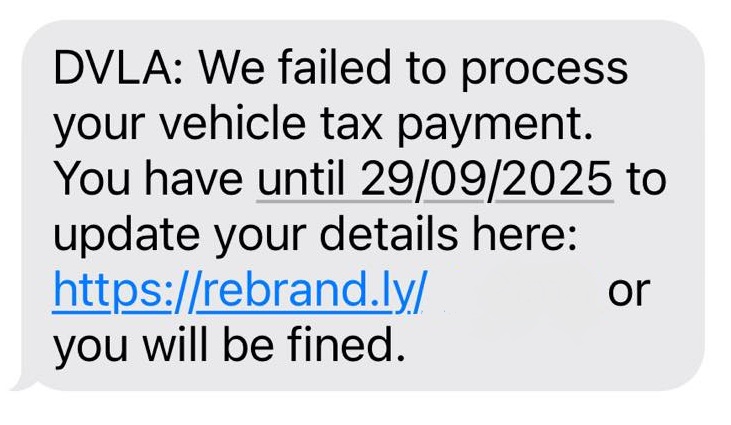
A scam text impersonating the Driver and Vehicle Licensing Agency (DVLA) tells you that it's 'failed to process your vehicle tax payment.'
It includes a link to 'update your details,' which will lead to a phishing website intent on stealing your personal information.
Scam texts can be reported by forwarding them to 7726.
13 October
WhatsApp Gold scam and Martinelli
Reports of a resurgence of the WhatsApp Gold and Martinelli scam are circulating. The scam installs malware on your phone.
It begins with a WhatsApp message promoting a sham version of the messaging service called 'WhatsApp Gold,' which has special features that can be unlocked by clicking a link.
This link will lead to malware being downloaded to your device.
Another version of this scam features a message which warns of a video called 'Martinelli' installing malware to your device if opened. However, there is no evidence that this video exists.
You can report a WhatsApp message by selecting it in your conversation and tapping ‘report’.
To report the sender on WhatsApp, open up the chat, tap on the sender's contact details and select 'block and report'.
Apple impersonation text
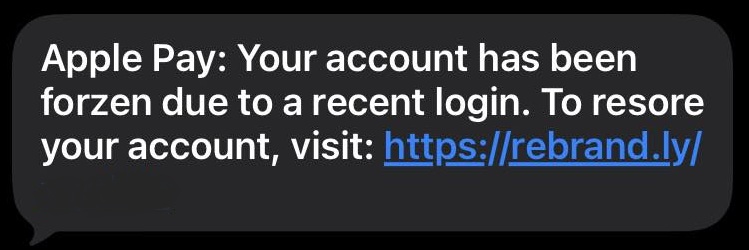
A scam text claiming to be from Apple tells you that your Apple Pay account has been frozen and provides a link to 'restore' it.
This link will lead to a dodgy website which will attempt to steal your personal and payment information.
Scam texts can be reported by forwarding them to 7726.
7 October
TV Licence scam email
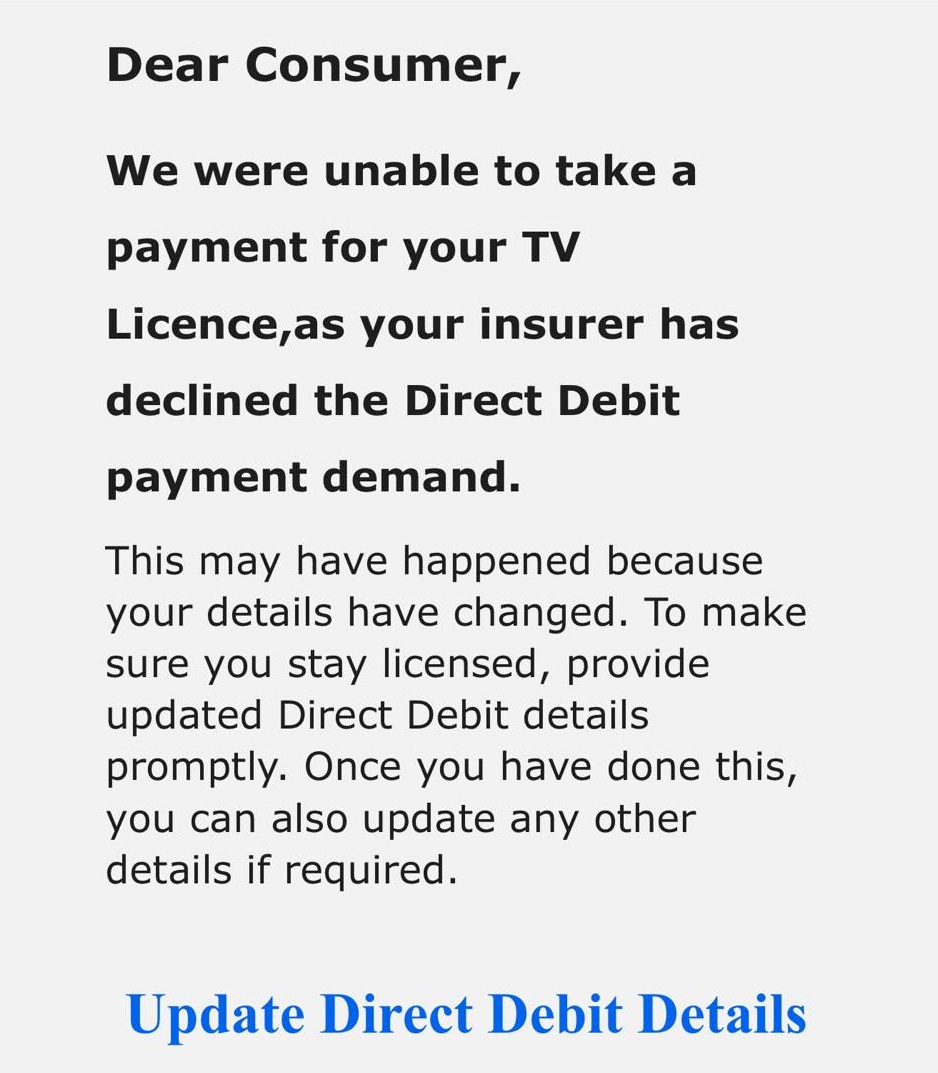
A dodgy email claiming to be from TV Licensing tells you that your direct debit payment has been declined.
It goes on to give you a link to update this, which will most likely lead to a site impersonating TV Licensing to get you to fill in your personal details.
Scam emails can be reported by forwarding them to report@phishing.gov.uk.
Suspicious websites can be reported to the National Cyber Security Centre.